Model impersonation doesn’t cease on the inbox. Whereas organizations have made vital progress securing their e mail domains with DMARC, attackers are exploiting an adjoining, less-defended floor: social media.
Fraudulent profiles on platforms like Fb, Instagram, LinkedIn, TikTok, YouTube, and X now mimic firm pages, impersonate executives, and redirect customers to phishing infrastructure. AI instruments have made it quicker and cheaper than ever to create convincing fakes at scale, and the barrier to entry retains dropping.
For safety groups, it is a visibility hole. Conventional area monitoring doesn’t prolong to social platforms, leaving organizations uncovered within the very areas the place clients and companions interact with their model every day.
Why social media is the subsequent impersonation frontier
Not like domain-based assaults, which require registering infrastructure and internet hosting phishing pages, social media impersonation is operationally easy. An attacker creates a profile utilizing an organization’s title, emblem, and branding. They copy govt headshots and bios. Inside minutes, a convincing pretend account exists on a significant platform with no technical footprint for conventional instruments to detect.
These accounts misdirect clients towards phishing websites and scams, impersonate executives to unfold misinformation or solicit delicate knowledge, and goal provide chain companions by means of profiles that seem to characterize authentic contacts. The assault floor is huge, unstructured, and sits exterior the scope of most current safety tooling.
When e mail and area defenses tighten, impersonation shifts to channels the place safety is thinner. Social media provides low friction, broad attain, and restricted accountability. A single fraudulent account can work together with 1000’s of customers earlier than it’s flagged, not to mention eliminated. Industries with high-value buyer relationships, from monetary companies to retail {and professional} companies, are seeing a gentle improve in social media-based model abuse.
Extending Cisco’s safety from e mail to social media
Cisco first partnered with Pink Sift to deliver DMARC safety to its clients by means of Pink Sift OnDMARC. That partnership expanded with Pink Sift Model Belief for lookalike area detection and takedown, making a full-spectrum protection.
Now, Model Belief’s latest add-on, Social Media Monitoring, is now obtainable by means of Cisco. This provides Cisco clients the power to detect and reply to fraudulent social media profiles that impersonate their firm or executives.
Cisco clients already depend on anti-phishing defenses to guard their inboxes. Social Media Monitoring extends that safety to a channel the place phishing is tougher to catch and more and more widespread. Pretend firm profiles lure clients towards phishing websites, scams, or malware. Pretend govt profiles exploit management belief to solicit delicate data or unfold misinformation. These are phishing assaults by one other title, simply delivered by means of social platforms as an alternative of e mail, and so they sit exterior the attain of conventional domain-focused or mail-based defenses.
Why Model Belief’s method works
Most organizations that try social media monitoring do it manually: operating periodic searches, counting on buyer experiences, or ready for platform-level detection that usually comes too late. Model Belief takes a distinct method by scanning hundreds of thousands of profiles repeatedly and making use of the identical AI-powered detection used for lookalike domains to the social media floor.
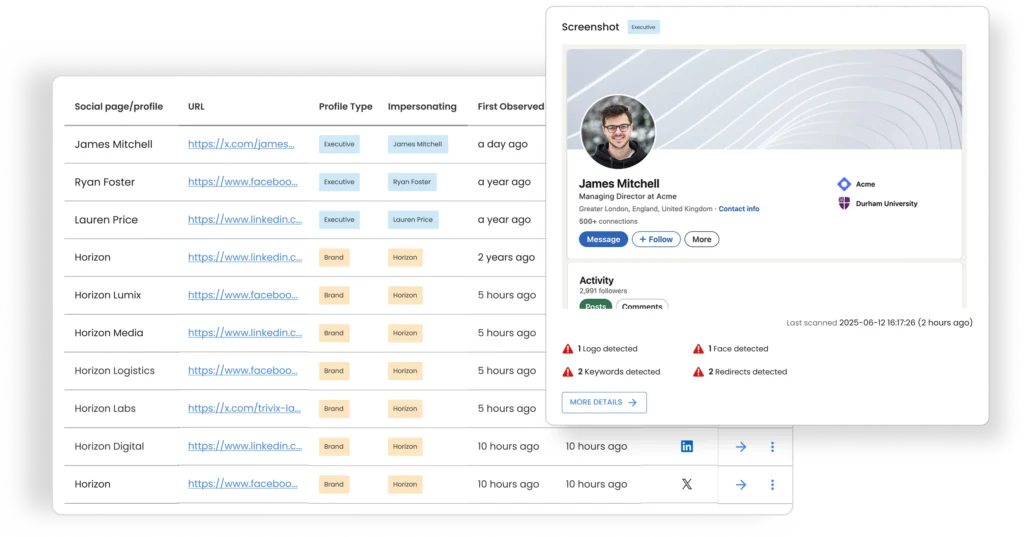
Reasonably than drowning groups in uncooked alerts, it surfaces solely the accounts value investigating, with sufficient context to make a quick classification determination. Takedown workflows are constructed into the identical interface already used for area safety, so groups can act on social impersonation threats with out switching instruments or including operational complexity. The result’s a constant detection-to-response course of throughout domains and social platforms, managed from a single view.
With OnDMARC for e mail authentication, Model Belief for lookalike area detection and now Social Media Monitoring for platform-based impersonation, Cisco clients have entry to layered model safety that covers the complete scope of how their model seems on-line and protects towards its abuse. One of the best half? Pink Sift’s product portfolio integrates inside current buyer ecosystems, complementing Cisco’s Safe E mail Menace Protection, permitting safety groups to function with full confidence and full visibility.
For extra data on area safety and Social Media Monitoring, please go to Pink Sift’s Cisco companion web page.
We’d love to listen to what you suppose! Ask a query and keep related with Cisco Safety on social media.
Cisco Safety Social Media